The enterprise adoption of AI agents is accelerating, moving beyond experimentation into core workflows. Companies like BNY are already deploying hundreds of 'digital workers,' with others seeing transformative success in development and customer support. This surge, however, amploys the risks associated with identity management.
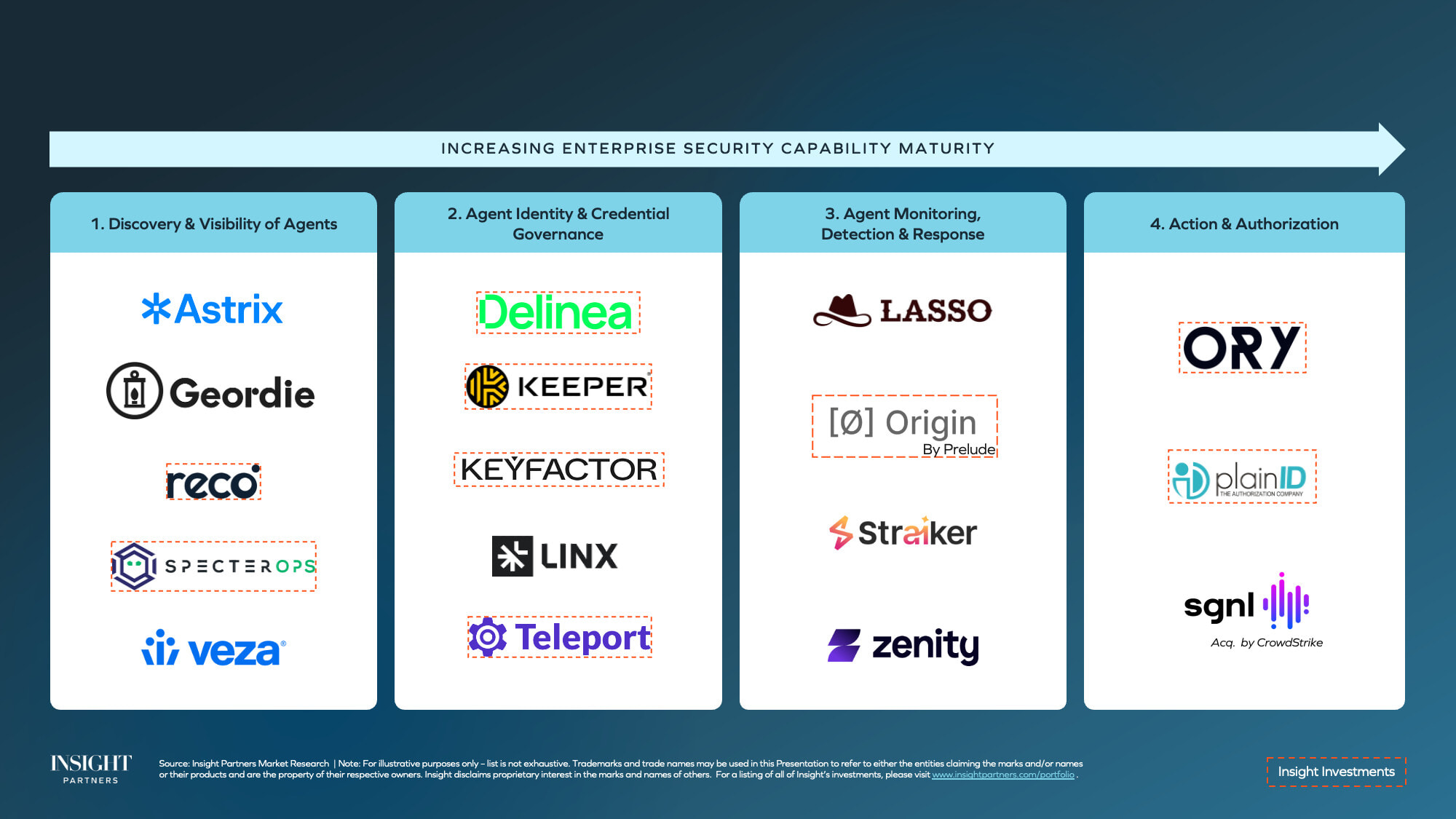
Recent threat reports highlight that identity has become the primary attack surface, with intrusions often blending into normal activity. AI agents, essentially non-human identities, introduce complex challenges for existing security frameworks. Poorly managed agent credentials and over-privileged identities present lucrative opportunities for threat actors. As Insight Partners notes, addressing AI agent identity and access management (Agent IAM) is the defining security topic for 2026.
Agents as Digital Employees: A Flawed Analogy
Many enterprises aim to treat AI agents like digital employees, assigning them unique identities and owners. While this addresses the 'identity' aspect, it falls short on 'access management.' The dynamic permissions required by agents, unlike predictable robotic process automation, pose a significant governance challenge.
Tracking delegated permissions and identifying the origination of actions through multi-hop delegation is complex. Current standards like OAuth are insufficient, pushing enterprises toward custom solutions or waiting for updated standards from bodies like the IETF. This problem is amplified by ephemeral agents that must inherit strict permissions from parent processes.