In the rapidly evolving world of technology, the only constant is change. This adage holds particularly true for cybersecurity, where the advent of quantum computing presents a significant, albeit future, threat to current cryptographic standards. Jeff Crume, a Distinguished Engineer at IBM, delves into this critical issue in a recent video, emphasizing the necessity of "crypto agility" to secure systems for the quantum era.
Understanding the Threat: Cryptography's Finite Lifespan
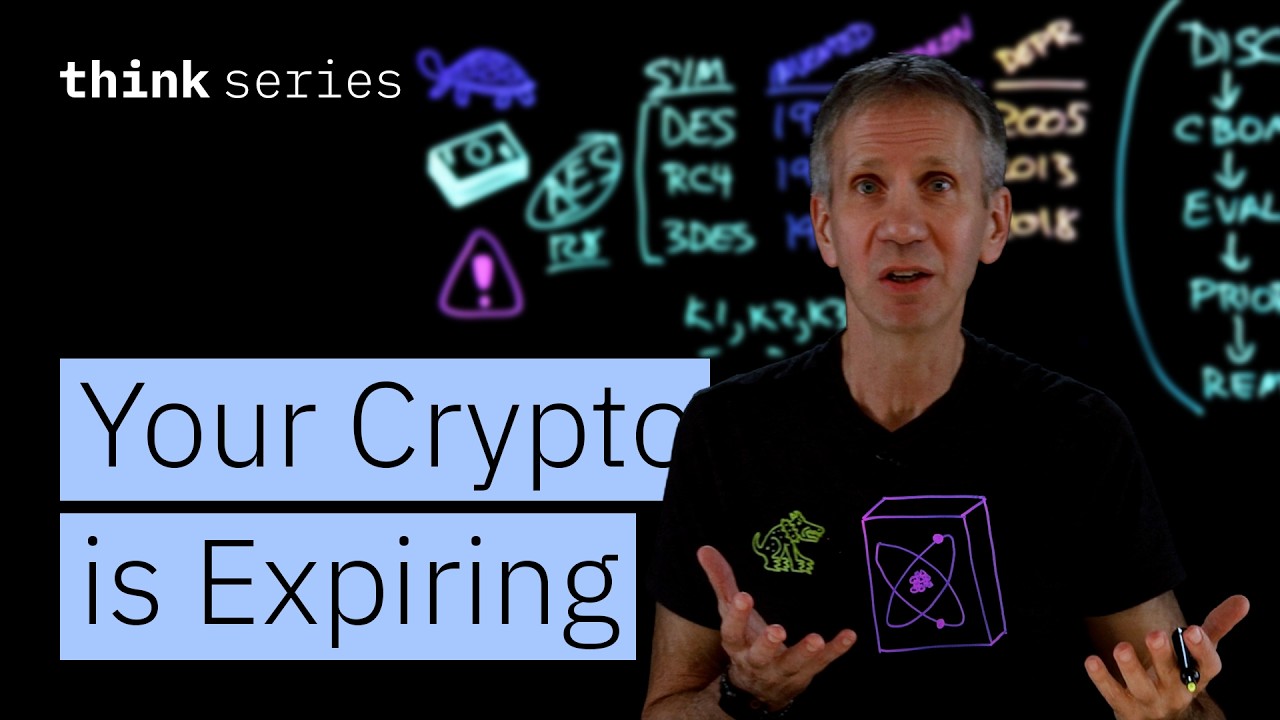
Crume begins by illustrating the cyclical nature of cryptographic algorithms. He highlights historical examples like DES (Data Encryption Standard), invented in 1977, which was the gold standard for many years but was eventually proven vulnerable and deprecated by 1998. Similarly, RC4, a widely used stream cipher invented in 1987, was later found to have significant weaknesses and was deprecated by 2013. These instances demonstrate that even robust cryptographic methods have a limited lifespan and will inevitably be superseded by more advanced techniques or due to discovered vulnerabilities.
The primary driver for this ongoing evolution is the relentless march of technological progress. As computing power increases, algorithms that were once considered secure can become susceptible to attack. The most significant impending shift, according to Crume, is the rise of quantum computers. These machines, with their fundamentally different approach to computation, are expected to break many of the asymmetric encryption algorithms currently in widespread use, posing a profound risk to data security.